aws-lambda
The aws-lambda plugin eases the integration of APISIX with AWS Lambda and Amazon API gateway to proxy for other AWS services.
The plugin supports authentication and authorization with AWS via IAM user credentials and API gateway's API key.
Examples
The examples below demonstrate how you can configure aws-lambda for different scenarios.
To follow along the examples, please first log into your AWS console and create a Lambda function with any runtime. You do not need to customize the function and by default, the function should return Hello from Lambda! when called.
Invoke Lambda Function Securely using IAM Access Keys
The following example demonstrates how you can integrate APISIX with the Lambda function and configure IAM access keys for authorization. The aws-lambda plugin implements AWS Signature Version 4 for IAM access keys. You will be first creating IAM access keys and the Lambda function URL on AWS console.
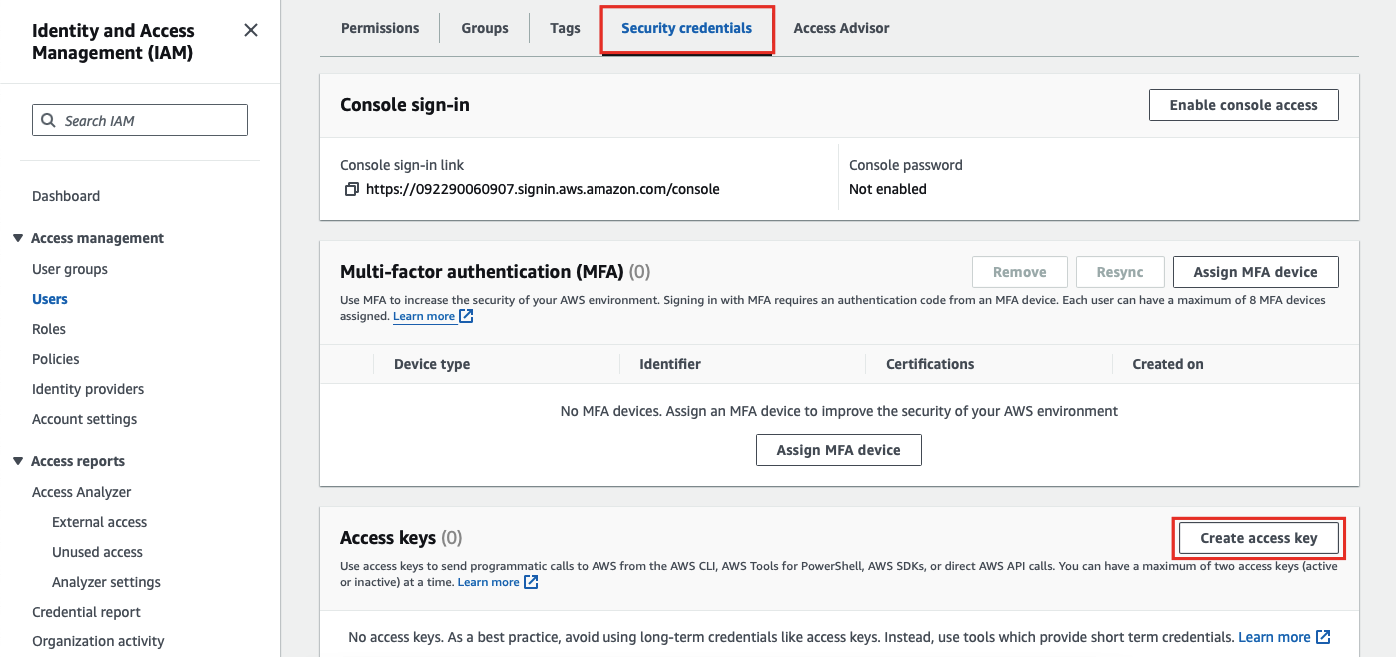
For IAM access keys, go to AWS Identity and Access Management (IAM) and click into the user you would like to use for integration.
Next, in the security credentials tab, select create access key:
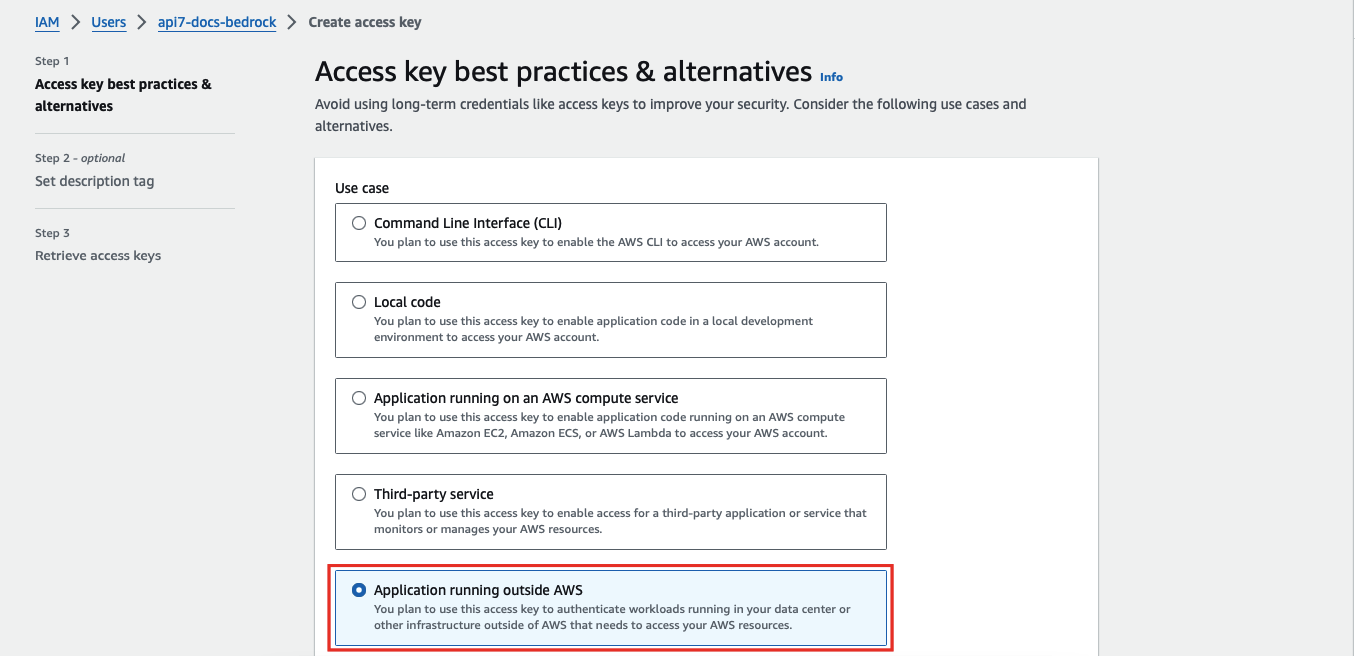
Select application running outside AWS as the use case:
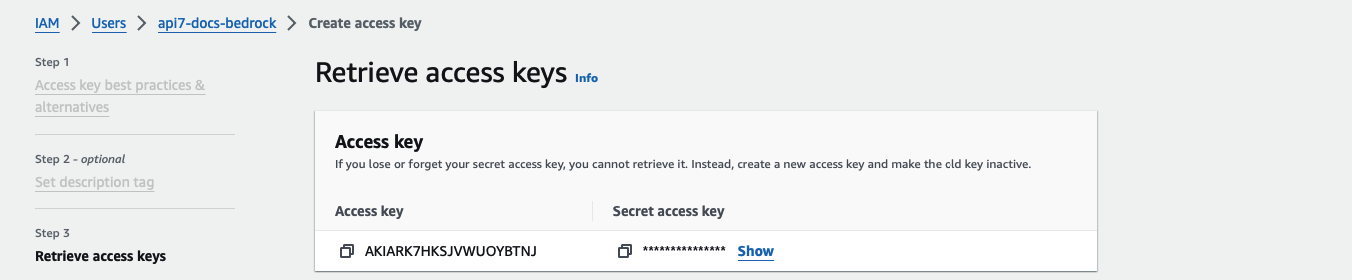
Continue the credential creation and note down the access key and secret access key:
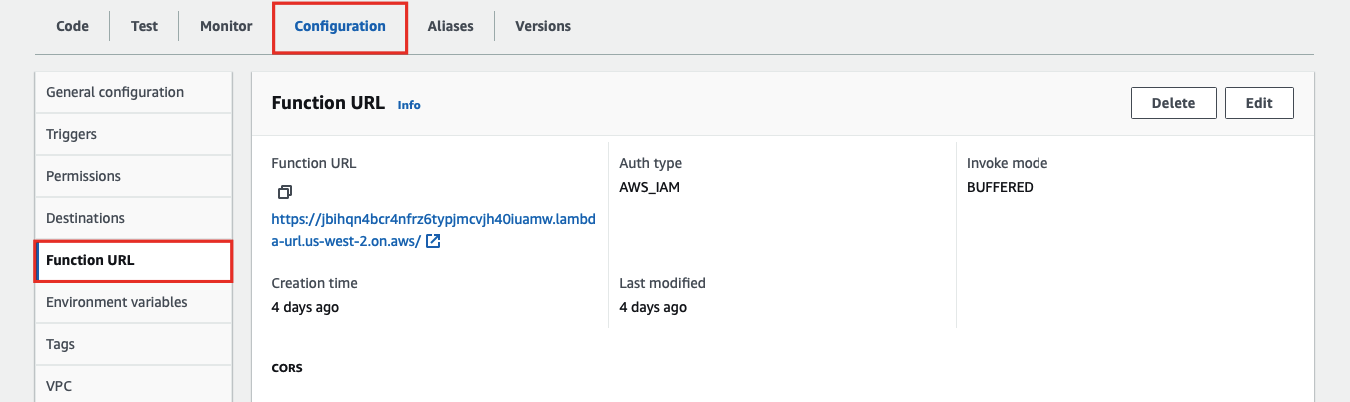
To create the Lambda function URL, go to the Configuration tab of the Lambda function and under Function URL, create a function URL:
Finally, create a route in APISIX with your function URL and IAM access keys:
- Admin API
- ADC
- Ingress Controller
curl "http://127.0.0.1:9180/apisix/admin/routes" -X PUT \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"id": "aws-lambda-route",
"uri": "/aws-lambda",
"plugins": {
"aws-lambda": {
"function_uri": "https://your-lambda-function-url.lambda-url.us-west-2.on.aws/",
"authorization": {
"iam": {
"accesskey": "YOUR_IAM_ACCESS_KEY",
"secretkey": "YOUR_IAM_SECRET_KEY",
"aws_region": "us-west-2",
"service": "lambda"
}
},
"ssl_verify": false
}
}
}'
services:
- name: aws-lambda-service
routes:
- name: aws-lambda-route
uris:
- /aws-lambda
plugins:
aws-lambda:
function_uri: https://your-lambda-function-url.lambda-url.us-west-2.on.aws/
authorization:
iam:
accesskey: YOUR_IAM_ACCESS_KEY
secretkey: YOUR_IAM_SECRET_KEY
aws_region: us-west-2
service: lambda
Synchronize the configuration to the gateway:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
apiVersion: apisix.apache.org/v1alpha1
kind: PluginConfig
metadata:
namespace: aic
name: aws-lambda-plugin-config
spec:
plugins:
- name: aws-lambda
config:
function_uri: https://your-lambda-function-url.lambda-url.us-west-2.on.aws/
authorization:
iam:
accesskey: YOUR_IAM_ACCESS_KEY
secretkey: YOUR_IAM_SECRET_KEY
aws_region: us-west-2
service: lambda
ssl_verify: false
---
apiVersion: gateway.networking.k8s.io/v1
kind: HTTPRoute
metadata:
namespace: aic
name: aws-lambda-route
spec:
parentRefs:
- name: apisix
rules:
- matches:
- path:
type: Exact
value: /aws-lambda
filters:
- type: ExtensionRef
extensionRef:
group: apisix.apache.org
kind: PluginConfig
name: aws-lambda-plugin-config
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: aic
name: aws-lambda-route
spec:
ingressClassName: apisix
http:
- name: aws-lambda-route
match:
paths:
- /aws-lambda
plugins:
- name: aws-lambda
enable: true
config:
function_uri: https://your-lambda-function-url.lambda-url.us-west-2.on.aws/
authorization:
iam:
accesskey: YOUR_IAM_ACCESS_KEY
secretkey: YOUR_IAM_SECRET_KEY
aws_region: us-west-2
service: lambda
ssl_verify: false
Apply the configuration:
kubectl apply -f aws-lambda-ic.yaml
❶ replace with your Lambda function URL
❷ replace with your IAM access key
❸ replace with your IAM secret access key
❹ replace with the AWS region of your Lambda function
❺ set to lambda when integrating with Lambda function
Send a request to the route:
curl -i "http://127.0.0.1:9080/aws-lambda"
You should receive an HTTP/1.1 200 OK response with the following message:
"Hello from Lambda!"
Integrate with Amazon API Gateway Securely with API Key
The following example demonstrates how you can integrate APISIX with Amazon API gateway and configure the gateway to trigger the execution of Lambda function.
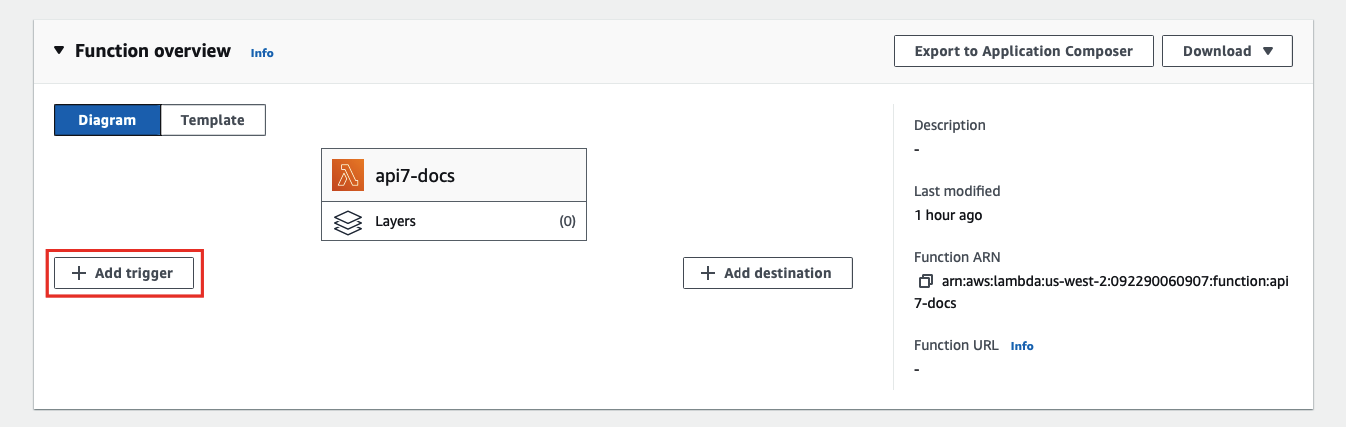
To configure an API gateway as a Lambda trigger, go to your Lambda function and select Add trigger:
Next, select API Gateway as the trigger and REST API as the API type, and finish adding the trigger:
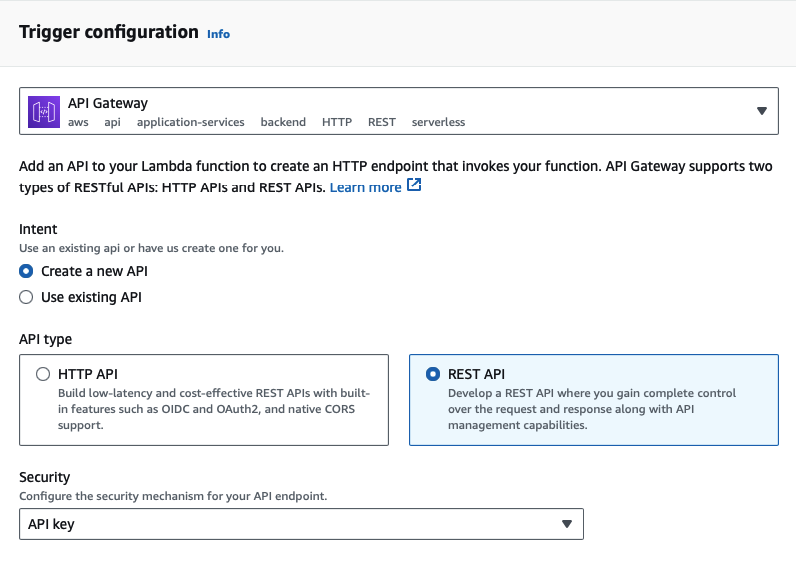
Amazon API Gateway supports HTTP APIs and REST APIs. API key support is available only for REST APIs, which is why this example uses a REST API trigger.
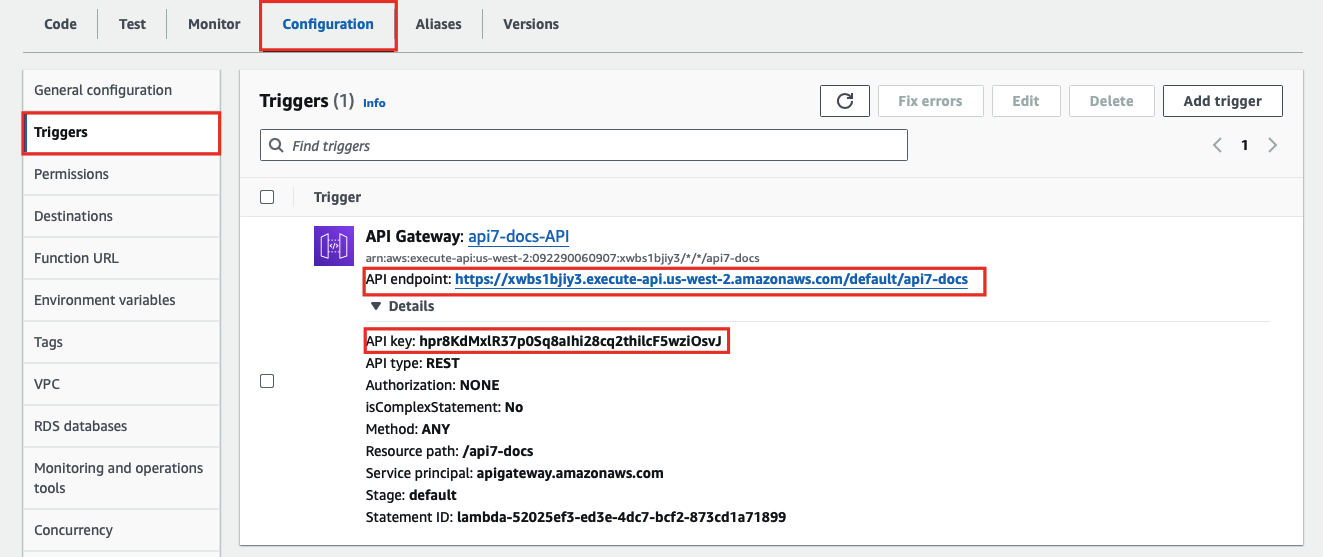
You should now be redirected back to the Lambda interface. To find the API key and gateway API endpoint, go to the Configuration tab of the Lambda function and under Triggers, you can find the details of the API gateway:
Finally, create a route in APISIX with your gateway endpoint and API key:
- Admin API
- ADC
- Ingress Controller
curl "http://127.0.0.1:9180/apisix/admin/routes" -X PUT \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"id": "aws-lambda-route",
"uri": "/aws-lambda",
"plugins": {
"aws-lambda": {
"function_uri": "https://your-api-id.execute-api.us-west-2.amazonaws.com/default/your-resource",
"authorization": {
"apikey": "YOUR_API_GATEWAY_API_KEY"
},
"ssl_verify": false
}
}
}'
services:
- name: aws-lambda-service
routes:
- name: aws-lambda-route
uris:
- /aws-lambda
plugins:
aws-lambda:
function_uri: https://your-api-id.execute-api.us-west-2.amazonaws.com/default/your-resource
authorization:
apikey: YOUR_API_GATEWAY_API_KEY
ssl_verify: false
Synchronize the configuration to the gateway:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
apiVersion: apisix.apache.org/v1alpha1
kind: PluginConfig
metadata:
namespace: aic
name: aws-lambda-plugin-config
spec:
plugins:
- name: aws-lambda
config:
function_uri: https://your-api-id.execute-api.us-west-2.amazonaws.com/default/your-resource
authorization:
apikey: YOUR_API_GATEWAY_API_KEY
ssl_verify: false
---
apiVersion: gateway.networking.k8s.io/v1
kind: HTTPRoute
metadata:
namespace: aic
name: aws-lambda-route
spec:
parentRefs:
- name: apisix
rules:
- matches:
- path:
type: Exact
value: /aws-lambda
filters:
- type: ExtensionRef
extensionRef:
group: apisix.apache.org
kind: PluginConfig
name: aws-lambda-plugin-config
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: aic
name: aws-lambda-route
spec:
ingressClassName: apisix
http:
- name: aws-lambda-route
match:
paths:
- /aws-lambda
plugins:
- name: aws-lambda
enable: true
config:
function_uri: https://your-api-id.execute-api.us-west-2.amazonaws.com/default/your-resource
authorization:
apikey: YOUR_API_GATEWAY_API_KEY
ssl_verify: false
Apply the configuration:
kubectl apply -f aws-lambda-ic.yaml
Send a request to the route:
curl -i "http://127.0.0.1:9080/aws-lambda"
You should receive an HTTP/1.1 200 OK response with the following message:
"Hello from Lambda!"
If your API key is invalid, you should receive an HTTP/1.1 403 Forbidden response.
Forward Requests to Amazon API Gateway Sub-Paths
The following example demonstrates how you can forward requests to a sub-path of the Amazon API gateway API and configure the API to trigger the execution of Lambda function.
Please follow the previous example to set up an API gateway first.
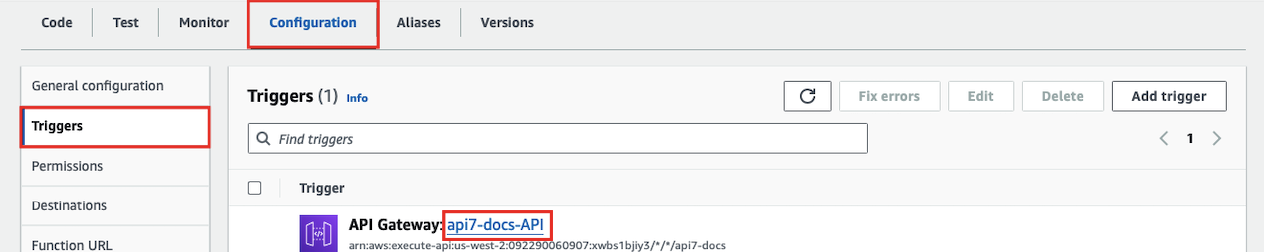
To create a sub-path, go to the Configuration tab of the Lambda function and under Triggers, click into the API gateway:
Next, select Create resource to create a sub-path:
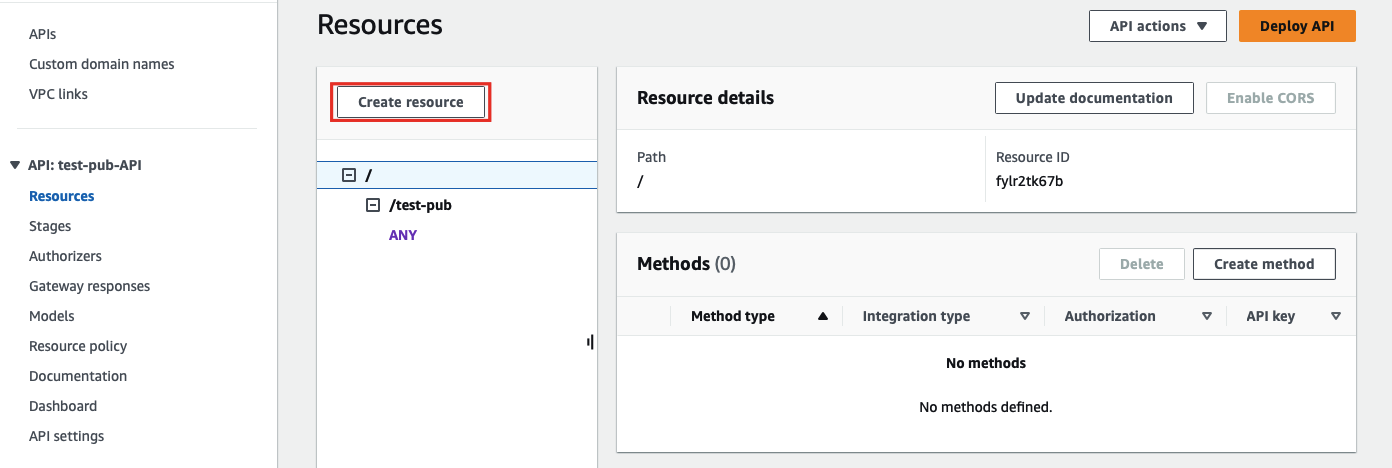
Enter the sub-path information and complete creation:
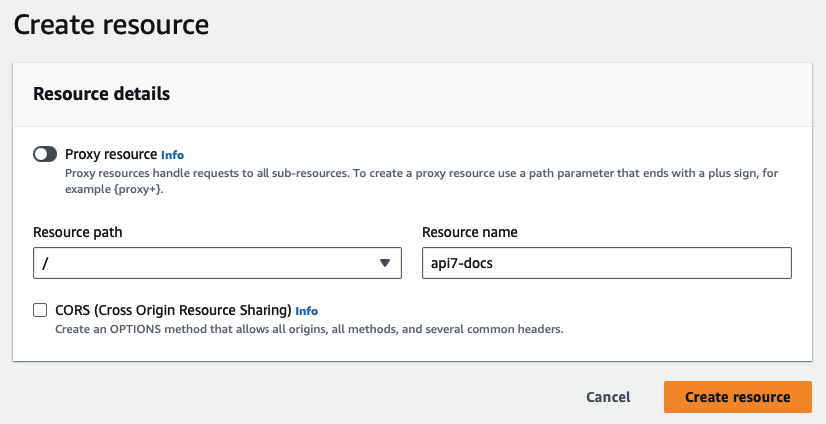
Once redirected back to the main gateway console, you should see the newly created path. Select Create method to configure HTTP methods for the path and the associated action:
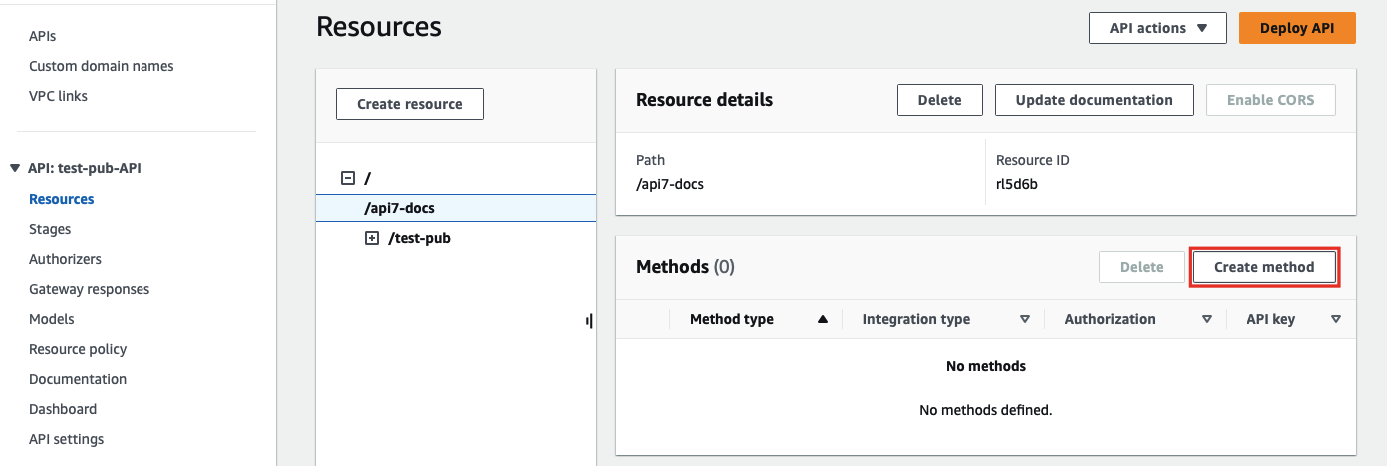
Select the allowed HTTP method in the dropdown. For the purpose of demonstration, this example continues to use the same Lambda function as the triggered action when the path is requested:
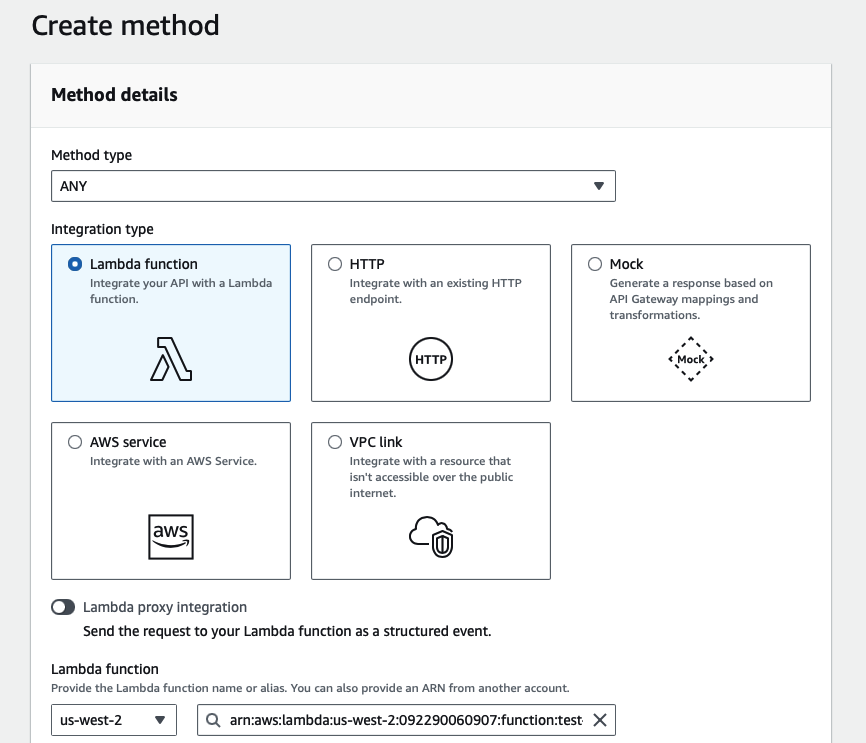
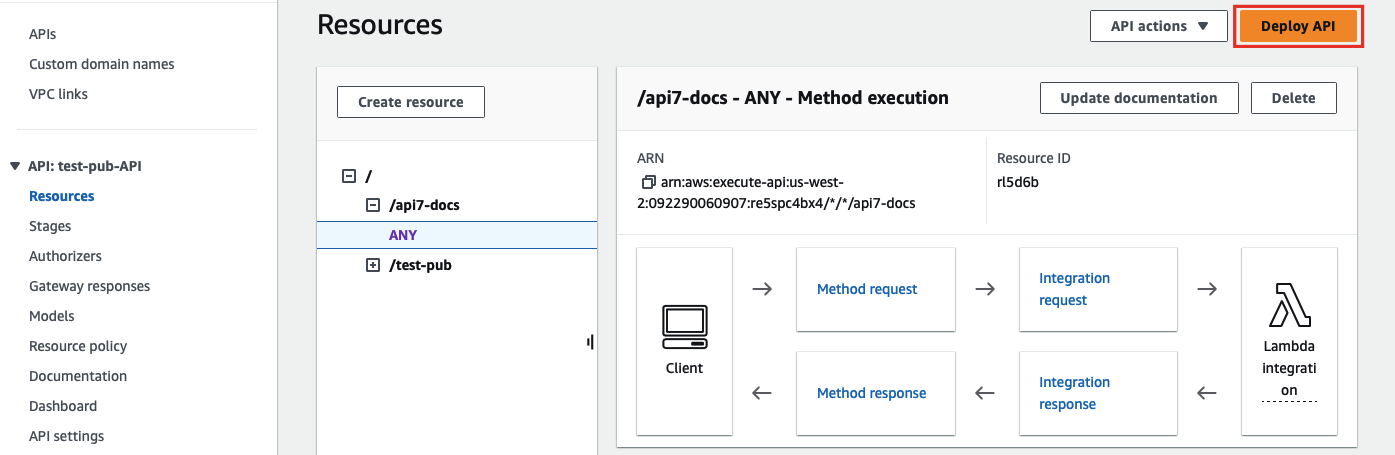
Finish the method creation. Once redirected back to the main gateway console, click on Deploy API to deploy the path and method changes:
Finally, create a route in APISIX with your gateway endpoint and API key:
- Admin API
- ADC
- Ingress Controller
curl "http://127.0.0.1:9180/apisix/admin/routes" -X PUT \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"id": "aws-lambda-route",
"uri": "/aws-lambda/*",
"plugins": {
"aws-lambda": {
"function_uri": "https://your-api-id.execute-api.us-west-2.amazonaws.com/default",
"authorization": {
"apikey": "YOUR_API_GATEWAY_API_KEY"
},
"ssl_verify": false
}
}
}'
services:
- name: aws-lambda-service
routes:
- name: aws-lambda-route
uris:
- /aws-lambda/*
plugins:
aws-lambda:
function_uri: https://your-api-id.execute-api.us-west-2.amazonaws.com/default
authorization:
apikey: YOUR_API_GATEWAY_API_KEY
ssl_verify: false
Synchronize the configuration to the gateway:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
apiVersion: apisix.apache.org/v1alpha1
kind: PluginConfig
metadata:
namespace: aic
name: aws-lambda-plugin-config
spec:
plugins:
- name: aws-lambda
config:
function_uri: https://your-api-id.execute-api.us-west-2.amazonaws.com/default
authorization:
apikey: YOUR_API_GATEWAY_API_KEY
ssl_verify: false
---
apiVersion: gateway.networking.k8s.io/v1
kind: HTTPRoute
metadata:
namespace: aic
name: aws-lambda-route
spec:
parentRefs:
- name: apisix
rules:
- matches:
- path:
type: PathPrefix
value: /aws-lambda/
filters:
- type: ExtensionRef
extensionRef:
group: apisix.apache.org
kind: PluginConfig
name: aws-lambda-plugin-config
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: aic
name: aws-lambda-route
spec:
ingressClassName: apisix
http:
- name: aws-lambda-route
match:
paths:
- /aws-lambda/*
plugins:
- name: aws-lambda
enable: true
config:
function_uri: https://your-api-id.execute-api.us-west-2.amazonaws.com/default
authorization:
apikey: YOUR_API_GATEWAY_API_KEY
ssl_verify: false
Apply the configuration:
kubectl apply -f aws-lambda-ic.yaml
❶ match all sub-paths of /aws-lambda/
❷ For Admin API, ADC, and APISIX CRD examples, the sub-paths matched by the wildcard * will be appended to the end of the function_uri. In the Gateway API example, PathPrefix matches requests under /aws-lambda/, so the forwarded request path continues after the configured function_uri prefix.
Send a request to the route:
curl -i "http://127.0.0.1:9080/aws-lambda/api7-docs"
APISIX will forward the request to https://your-api-id.execute-api.us-west-2.amazonaws.com/default/api7-docs and you should receive an HTTP/1.1 200 OK response with the following message:
"Hello from Lambda!"
If your API key is invalid or if the requested path is not associated with any method, you should receive an HTTP/1.1 403 Forbidden response.