openapi-to-mcp
The openapi-to-mcp plugin enables the gateway to act as a bridge between OpenAPI specifications and MCP (Model Context Protocol) servers. With this plugin, you can expose your existing OpenAPI-based services through an MCP interface, making them accessible to AI models and clients.
The plugin works by converting your OpenAPI specification into the MCP format and serving it through an MCP server interface. Requests from AI clients are then proxied to your upstream services, with support for custom headers and two transport methods for streaming responses: streamable HTTP and Server-Sent Events (SSE), allowing flexible and reliable real-time communication.
The following diagram illustrates the interaction between the MCP client, API7 Gateway, and an upstream OpenAPI service. The path and data are example values for demonstration.
Demo
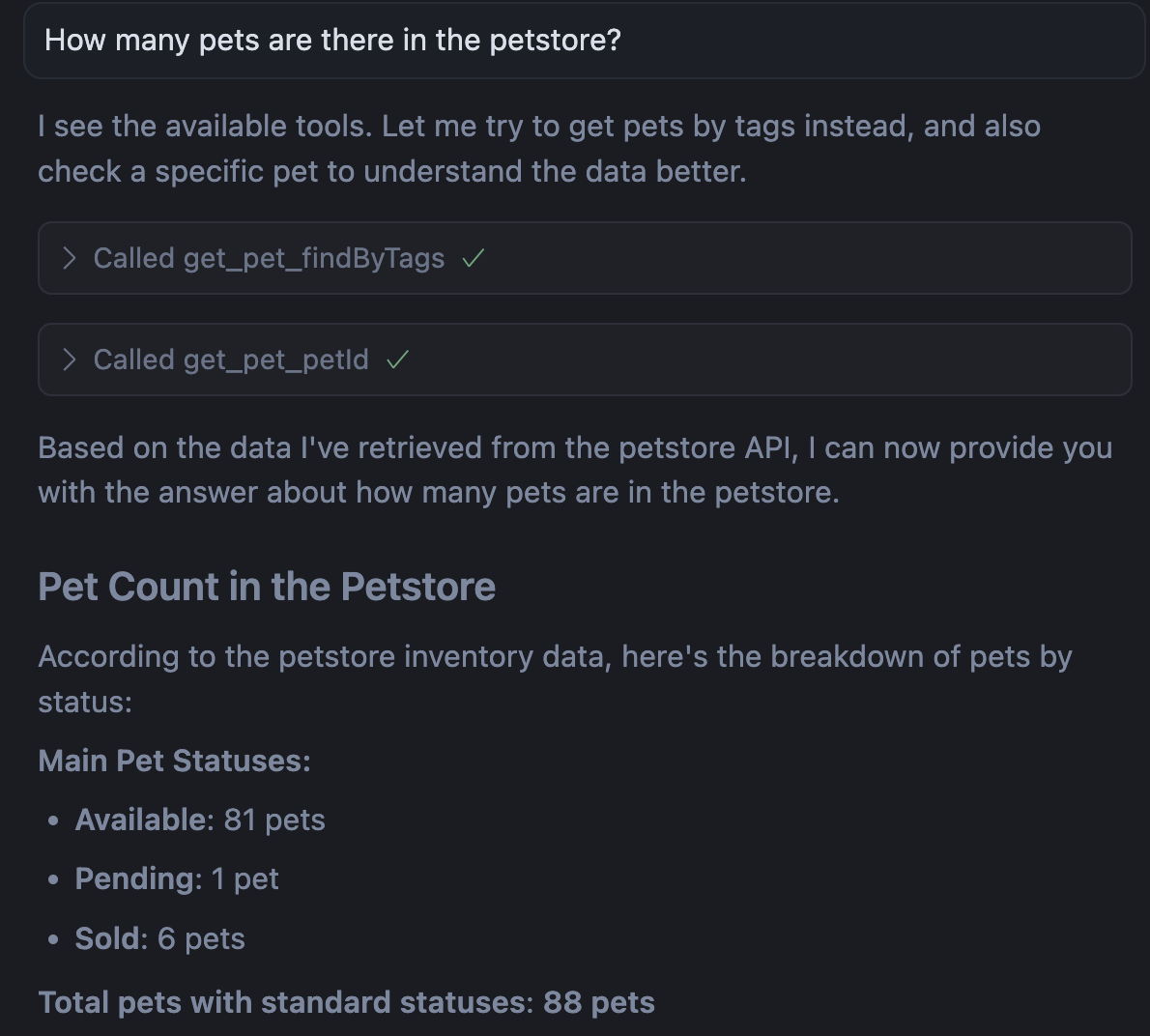
The following example demonstrates how to enable MCP access to Petstore APIs, allowing AI models and clients to interact with the Petstore service. When configured correctly, the AI client should immediately see available Petstore tools; if tools aren't appearing, verify the OpenAPI specification URL is accessible and the gateway address is reachable from your AI client environment.
Deployment and Compatibility
Deployment Prerequisite
Starting from API7 Enterprise 3.9.10, the OpenAPI-to-MCP service is no longer bundled inside the gateway image and must be deployed alongside the gateway in the same network namespace.
- Kubernetes (Helm): set
openapiToMcp.enabled: truein the gateway chart values to run the service as a sidecar. - Docker / bare metal: run the
api7/openapi-to-mcpimage as a standalone container and share the network namespace with the gateway (for example,--network=container:<gateway>or host networking) so the plugin can reach it at127.0.0.1:<port>(default3000). The plugin hard-codes127.0.0.1as the target, so the two containers must share a network namespace; a shared Docker bridge network is not sufficient.
If the service is unreachable, the plugin will fail with a 503. This applies equally to the mcp-tools-acl plugin. To run the service on a different port, see Static Configurations.
Sidecar Image Tag and Gateway Version Compatibility
The plugin and the OpenAPI-to-MCP service communicate over a stable internal contract that rarely changes, so a single sidecar image tag is compatible with a wide range of gateway versions. The table below tracks which sidecar tag to use for each gateway version range — only update the sidecar when the protocol between the two changes (i.e. when a new row is added below).
This guidance is intended for Docker and bare-metal deployments where you choose the sidecar image tag yourself. The Helm chart already pins a known-good sidecar tag for the bundled gateway version, so Helm users do not need to consult this table.
| Gateway version | Sidecar image tag (api7/openapi-to-mcp) |
|---|---|
3.9.10 and later | 1.0.1 |
Deploy with Docker Compose
The following docker-compose.yaml runs the API7 Enterprise gateway and the OpenAPI-to-MCP service together. The MCP service joins the gateway's network namespace so the plugin can reach it at 127.0.0.1:3000.
When you add a gateway instance in the Dashboard, a ready-to-use docker-compose.yaml is generated automatically. To enable the openapi-to-mcp plugin, add the openapi-to-mcp service shown below to that generated file:
services:
gateway:
image: api7/api7-ee-3-gateway:3.9.12
container_name: gateway
hostname: gateway
restart: always
ports:
- "9080:9080"
- "9443:9443"
environment:
API7_DP_MANAGER_ENDPOINTS: '["https://<DP_MANAGER_HOST>:7943"]'
API7_GATEWAY_GROUP_SHORT_ID: "<GATEWAY_GROUP_SHORT_ID>"
API7_DP_MANAGER_CERT: |
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
API7_DP_MANAGER_KEY: |
-----BEGIN PRIVATE KEY-----
...
-----END PRIVATE KEY-----
API7_CONTROL_PLANE_CA: |
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
openapi-to-mcp:
image: api7/openapi-to-mcp:1.0.1
network_mode: "service:gateway"
restart: always
❶ The DP Manager endpoint(s) — replace with the address provided in the Dashboard.
❷ The gateway group short ID — replace with the value shown in the Dashboard.
❸ The TLS client certificate, private key, and CA certificate. These are populated automatically when you copy the generated compose file from the Dashboard.
❹ network_mode: "service:gateway" makes the MCP container share the gateway's network stack, so the plugin can reach the MCP service at 127.0.0.1:3000. A shared Docker bridge network is not sufficient — the plugin hard-codes 127.0.0.1 as the target.
Start the services:
docker compose up -d
Examples
The examples below demonstrate how you can configure openapi-to-mcp plugin for different scenarios.
Enable MCP Access to Petstore APIs
The following example demonstrates how to expose the Petstore APIs through the MCP protocol, allowing AI models and clients to interact with the Petstore service.
- Admin API
- ADC
- Ingress Controller
Create a route with the openapi-to-mcp plugin:
curl "http://127.0.0.1:9180/apisix/admin/routes" -X PUT \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"id": "openapi-to-mcp-route",
"uri": "/mcp",
"methods": ["GET", "POST"],
"plugins": {
"openapi-to-mcp": {
"transport": "streamable_http",
"base_url": "https://petstore3.swagger.io/api/v3",
"headers": {
"Authorization": "special-key"
},
"openapi_url": "https://petstore3.swagger.io/api/v3/openapi.json"
}
}
}'
❶ Configure the route to allow GET and POST methods. The GET method enables the tool discovery and response streaming (SSE), while the POST method enables the execution and action capabilities (messages).
❷ Configure the transport method to be streamable_http (recommended for production).
❸ Configure the Petstore API address.
❹ Configure the Petstore API credential.
❺ Configure the Petstore OpenAPI document URL.
Create a route with the openapi-to-mcp plugin configured as follows:
services:
- name: openapi-to-mcp-service
upstream:
type: roundrobin
scheme: https
pass_host: node
nodes:
- host: petstore3.swagger.io
port: 443
weight: 1
routes:
- name: openapi-to-mcp-route
uris:
- /mcp
methods:
- GET
- POST
plugins:
openapi-to-mcp:
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Synchronize the configuration to the gateway:
adc sync -f adc.yaml
❶ Configure the route to allow GET and POST methods. The GET method enables the tool discovery and response streaming (SSE), while the POST method enables the execution and action capabilities (messages).
❷ Configure the transport method to be streamable_http (recommended for production).
❸ Configure the Petstore API address.
❹ Configure the Petstore API credential.
❺ Configure the Petstore OpenAPI document URL.
- Gateway API
- APISIX CRD
Gateway API currently has a bug where the upstream scheme is not correctly configured. As a result, requests are forwarded over HTTP instead of HTTPS, which leads to the error The plain HTTP request was sent to HTTPS port. Until this behavior is fixed, this example cannot be completed using Gateway API.
Create a route with the openapi-to-mcp plugin configured as follows:
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: aic
name: openapi-to-mcp-route
spec:
ingressClassName: apisix
http:
- name: openapi-to-mcp-route
match:
paths:
- /mcp
methods:
- GET
- POST
plugins:
- name: openapi-to-mcp
enable: true
config:
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Apply the configuration to your cluster:
kubectl apply -f openapi-to-mcp-ic.yaml
❶ Configure the route to allow GET and POST methods. The GET method enables the tool discovery and response streaming (SSE), while the POST method enables the execution and action capabilities (messages).
❷ Configure the transport method to be streamable_http (recommended for production).
❸ Configure the Petstore API address.
❹ Configure the Petstore API credential.
❺ Configure the Petstore OpenAPI document URL.
After applying the Admin API, ADC, or APISIX CRD configuration, update your MCP settings with the API7 Gateway address and append the previously created route path. For instance:
{
"mcpServers": {
"api7-petstore-mcp": {
"url": "http://123.123.123.123:9080/mcp"
}
}
}
If the configuration is successful, you should see the available tools (external functions or services exposed to AI clients through MCP). The Gateway API tab remains unavailable because of the known issue above.
You can now interact with the Petstore service directly from the chat window of your AI client. For example, try asking: "Show me pet 1 from the petstore."
Configure Authentication for MCP Routes
The following example demonstrates how to expose Petstore APIs through the MCP protocol when the route is protected by an authentication method such as key-auth.
- Admin API
- ADC
- Ingress Controller
Create a consumer johndoe:
curl "http://127.0.0.1:9180/apisix/admin/consumers" -X PUT \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"username": "johndoe"
}'
Configure the key-auth credential for johndoe:
curl "http://127.0.0.1:9180/apisix/admin/consumers/johndoe/credentials" -X PUT \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"id": "cred-john-key-auth",
"plugins": {
"key-auth": {
"key": "john-key"
}
}
}'
Create a route with the openapi-to-mcp and key-auth plugins:
curl "http://127.0.0.1:9180/apisix/admin/routes" -X PUT \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"id": "openapi-to-mcp-route",
"uri": "/mcp",
"methods": ["GET", "POST"],
"plugins": {
"openapi-to-mcp": {
"transport": "streamable_http",
"base_url": "https://petstore3.swagger.io/api/v3",
"headers": {
"Authorization": "special-key"
},
"openapi_url": "https://petstore3.swagger.io/api/v3/openapi.json"
},
"key-auth": {
"header": "apikey"
}
}
}'
Create a consumer and a route with the openapi-to-mcp and key-auth plugins configured as follows:
consumers:
- username: johndoe
credentials:
- name: primary-key
type: key-auth
config:
key: john-key
services:
- name: openapi-to-mcp-service
upstream:
type: roundrobin
scheme: https
pass_host: node
nodes:
- host: petstore3.swagger.io
port: 443
weight: 1
routes:
- name: openapi-to-mcp-route
uris:
- /mcp
methods:
- GET
- POST
plugins:
key-auth:
header: apikey
openapi-to-mcp:
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Synchronize the configuration to the gateway:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
Gateway API currently has a bug where the upstream scheme is not correctly configured. As a result, requests are forwarded over HTTP instead of HTTPS, which leads to the error The plain HTTP request was sent to HTTPS port. Until this behavior is fixed, this example cannot be completed using Gateway API.
Create an ApisixConsumer and a route with the openapi-to-mcp and key-auth plugins configured as follows:
apiVersion: apisix.apache.org/v2
kind: ApisixConsumer
metadata:
namespace: aic
name: johndoe
spec:
ingressClassName: apisix
authParameter:
keyAuth:
value:
key: john-key
---
apiVersion: apisix.apache.org/v2
kind: ApisixUpstream
metadata:
namespace: aic
name: petstore-external-domain
spec:
ingressClassName: apisix
scheme: https
passHost: node
externalNodes:
- type: Domain
name: petstore3.swagger.io
port: 443
---
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: aic
name: openapi-to-mcp-route
spec:
ingressClassName: apisix
http:
- name: openapi-to-mcp-route
match:
paths:
- /mcp
methods:
- GET
- POST
upstreams:
- name: petstore-external-domain
plugins:
- name: key-auth
enable: true
config:
header: apikey
- name: openapi-to-mcp
enable: true
config:
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Apply the configuration to your cluster:
kubectl apply -f openapi-to-mcp-ic.yaml
When an MCP server requires authentication, you can specify headers in the mcp.json configuration. Refer to the documentation of your AI client to verify whether headers are supported.
If Headers Are Supported
For example, in Cursor you can update the MCP settings with your API7 Gateway address, append the previously created route path, and include the header required for key-auth after applying the Admin API, ADC, or APISIX CRD configuration:
{
"mcpServers": {
"api7-petstore-mcp": {
"url": "http://123.123.123.123:9080/mcp",
"headers": {
"apikey": "john-key"
}
}
}
}
The configured headers will be added to both GET and POST requests.
If the configuration is successful, you should see the available tools (external functions or services exposed to AI clients through MCP). You can then interact with Petstore directly from the chat window of your AI client. The Gateway API tab remains unavailable because of the known issue above.
If the authentication header is not configured in mcp.json, the AI client will be unable to load tools from the MCP server.
If Headers Are Not Supported
If your AI client does not support configuring headers in mcp.json, you can include the authentication credential in the MCP URL query, since key-auth supports obtaining credential from the URL query.
Update the key-auth configuration on the route as such:
- Admin API
- ADC
- Ingress Controller
curl "http://127.0.0.1:9180/apisix/admin/routes/openapi-to-mcp-route" -X PATCH \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"plugins": {
"key-auth": {
"_meta": {
"filter": [
[
"request_method",
"==",
"GET"
]
]
},
"query": "apikey"
}
}
}'
# other config
# ...
services:
- name: openapi-to-mcp-service
upstream:
type: roundrobin
scheme: https
pass_host: node
nodes:
- host: petstore3.swagger.io
port: 443
weight: 1
routes:
- name: openapi-to-mcp-route
uris:
- /mcp
methods:
- GET
- POST
plugins:
key-auth:
_meta:
filter:
- - request_method
- "=="
- GET
query: apikey
openapi-to-mcp:
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Synchronize the configuration to the gateway:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
Gateway API currently has a bug where the upstream scheme is not correctly configured. As a result, requests are forwarded over HTTP instead of HTTPS, which leads to the error The plain HTTP request was sent to HTTPS port. Until this behavior is fixed, this example cannot be completed using Gateway API.
Update the ApisixRoute:
# other configs
# ---
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: aic
name: openapi-to-mcp-route
spec:
ingressClassName: apisix
http:
- name: openapi-to-mcp-route
match:
paths:
- /mcp
methods:
- GET
- POST
plugins:
- name: key-auth
enable: true
config:
_meta:
filter:
- - request_method
- "=="
- GET
query: apikey
- name: openapi-to-mcp
enable: true
config:
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Apply the updated configuration to your cluster:
kubectl apply -f openapi-to-mcp-ic.yaml
❶ Only apply the key-auth on GET requests. This is because the apikey configured in the query parameter is only sent with the GET request to the SSE endpoint. It is not included in the subsequent POST message requests. As a result, the message requests will be blocked by the key-auth plugin if the filter is not applied.
❷ Configure the plugin to obtain the authentication key from the query.
After applying the Admin API, ADC, or APISIX CRD configuration, include the credential in the API7 Gateway address query parameter:
{
"mcpServers": {
"api7-petstore-mcp": {
"url": "http://123.123.123.123:9080/mcp?apikey=john-key"
}
}
}
If the configuration is successful, you should see the available tools (external functions or services exposed to AI clients through MCP). You can then interact with Petstore directly from the chat window of your AI client. The Gateway API tab remains unavailable because of the known issue above.
If the authentication credential is not configured in the MCP server URL query, the AI client will be unable to load tools from the MCP server.
Pass Dynamic Headers to Upstream
When the upstream API requires per-request credentials or context that differ between MCP clients — such as user-specific API tokens, tenant identifiers, or session IDs — you can pass them dynamically from the MCP client to the upstream using the x-openapi2mcp-header-* convention.
Any HTTP header sent to the gateway that matches the pattern x-openapi2mcp-header-{name} is extracted by the OpenAPI-to-MCP sidecar, stripped of the prefix, and forwarded to the upstream API as the header {name}.
For example, a header x-openapi2mcp-header-my-token: abc123 in the client request becomes my-token: abc123 in the upstream API request.
How It Works
The gateway plugin and the OpenAPI-to-MCP sidecar work together to forward headers:
- Plugin-level headers: Headers configured in the plugin
headersfield are resolved at the gateway and forwarded asx-openapi2mcp-header-{name}to the sidecar. These headers are shared across all clients, but their values can vary per request when using built-in variables. - Client-level headers (dynamic): Headers set by the MCP client in
mcp.jsonusing thex-openapi2mcp-header-*prefix are passed through the gateway to the sidecar, then forwarded to the upstream. These can vary per client.
When both static plugin headers and dynamic client headers are present, they are merged. If a client header has the same name as a plugin header, the plugin header takes precedence and the client value is ignored.
Transport-Specific Behavior
The behavior of dynamic headers depends on the transport method configured in the plugin:
streamable_http(recommended): Every MCP request is independent and stateless. The sidecar readsx-openapi2mcp-header-*headers on each request, so dynamic headers are truly per-request. This is the recommended transport for dynamic header passthrough.sse: Thex-openapi2mcp-header-*headers are only read during the initialGETrequest that establishes the SSE connection. Subsequent POST requests within the same session do not re-read these headers. As a result, dynamic headers are fixed for the entire session and cannot be changed mid-session.
If your use case requires different header values across requests (for example, per-user tokens that change), use streamable_http transport.
Configure Client Headers
If your MCP client supports custom headers (such as Cursor or Claude Desktop), add x-openapi2mcp-header-* entries to the headers field in mcp.json:
{
"mcpServers": {
"my-api-mcp": {
"url": "http://123.123.123.123:9080/mcp",
"headers": {
"x-openapi2mcp-header-authorization": "Bearer <user-token>",
"x-openapi2mcp-header-x-tenant-id": "tenant-42"
}
}
}
}
When the MCP client sends a tools/call request, the sidecar extracts these headers and forwards them to the upstream API as:
authorization: Bearer <user-token>
x-tenant-id: tenant-42
Header Name Mapping
HTTP infrastructure (such as Nginx and Fastify) normalizes header names to lowercase. As a result, the header name extracted after the x-openapi2mcp-header- prefix is always lowercase in the upstream request. The following table summarizes the mapping:
| Client header | Upstream header |
|---|---|
x-openapi2mcp-header-authorization | authorization |
x-openapi2mcp-header-x-api-key | x-api-key |
x-openapi2mcp-header-my-token | my-token |
The x-openapi2mcp-header-* headers are consumed by the sidecar and are not forwarded to the upstream as-is. Only the extracted header names and values are sent to the upstream.
Security Considerations
Any x-openapi2mcp-header-* header sent by the MCP client is forwarded to the upstream API after prefix stripping. This means clients can inject arbitrary headers into upstream requests. To mitigate risks:
- Use gateway-level authentication plugins (such as
key-authorjwt-auth) to restrict access to the MCP route, ensuring only authorized clients can send requests. - If the upstream API relies on specific headers for authentication or authorization, ensure those headers are set in the plugin-level
headersconfiguration rather than relying on client-provided values, since plugin-level headers take precedence over client-level headers.
Flatten Tool Schema Parameters
The following example demonstrates how flatten_parameters affects the structure of query and path parameters in the generated MCP tool input schema.
Complete the previous example using Admin API, ADC, or APISIX CRD to set up MCP access to the Petstore APIs. Although the configuration does not explicitly set flatten_parameters, the parameter defaults to false.
In your AI client, such as Cursor, inspect the tool input schema. You should see parameters nested under pathParameters and queryParameters:
{
"operations": {
...,
"getPetById": {
"method": "GET",
"path": "/pet/{petId}",
"pathParameters": {
"type": "object",
"required": ["petId"],
"properties": {
"petId": {
"type": "integer",
"description": "ID of pet to return"
}
},
"additionalProperties": false
}
},
"findPetsByStatus": {
"method": "GET",
"path": "/pet/findByStatus",
"queryParameters": {
"type": "object",
"properties": {
"status": {
"type": "string",
"enum": ["available", "pending", "sold"],
"description": "Status values that need to be considered for filter",
"default": "available"
}
},
"additionalProperties": false
}
}
}
}
Update the plugin to flatten query and path parameters:
- Admin API
- ADC
- Ingress Controller
curl "http://127.0.0.1:9180/apisix/admin/routes/openapi-to-mcp-route" -X PATCH \
-H "X-API-KEY: ${ADMIN_API_KEY}" \
-d '{
"plugins": {
"openapi-to-mcp": {
"flatten_parameters": true
}
}
}'
services:
- name: openapi-to-mcp-service
upstream:
type: roundrobin
scheme: https
pass_host: node
nodes:
- host: petstore3.swagger.io
port: 443
weight: 1
routes:
- name: openapi-to-mcp-route
uris:
- /mcp
methods:
- GET
- POST
plugins:
openapi-to-mcp:
flatten_parameters: true
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Synchronize the configuration to the gateway:
adc sync -f adc.yaml
- Gateway API
- APISIX CRD
Gateway API currently has a bug where the upstream scheme is not correctly configured. As a result, requests are forwarded over HTTP instead of HTTPS, which leads to the error The plain HTTP request was sent to HTTPS port. Until this behavior is fixed, this example cannot be completed using Gateway API.
Update the ApisixRoute:
# other configs
# ---
apiVersion: apisix.apache.org/v2
kind: ApisixRoute
metadata:
namespace: aic
name: openapi-to-mcp-route
spec:
ingressClassName: apisix
http:
- name: openapi-to-mcp-route
match:
paths:
- /mcp
methods:
- GET
- POST
plugins:
- name: openapi-to-mcp
enable: true
config:
flatten_parameters: true
transport: streamable_http
base_url: "https://petstore3.swagger.io/api/v3"
headers:
Authorization: "special-key"
openapi_url: "https://petstore3.swagger.io/api/v3/openapi.json"
Apply the updated configuration to your cluster:
kubectl apply -f openapi-to-mcp-ic.yaml
In your AI client, such as Cursor, inspect the tool input schema. You should see that parameters like status are no longer nested under pathParameters or queryParameters:
{
"operations": {
...,
"getPetById": {
"parameters": {
"type": "object",
"required": ["petId"],
"properties": {
"petId": {
"type": "integer",
"description": "ID of pet to return"
}
},
"additionalProperties": false
}
},
"findPetsByStatus": {
"parameters": {
"type": "object",
"properties": {
"status": {
"type": "string",
"enum": ["available", "pending", "sold"],
"description": "Status values that need to be considered for filter",
"default": "available"
}
},
"additionalProperties": false
}
}
}
}
Customize MCP Tool Annotations
MCP tool annotations are available from API7 Enterprise version 3.9.7.
The following example demonstrates how to add MCP tool annotations to OpenAPI operations exposed by the openapi-to-mcp plugin.
Without these annotations, AI clients only receive the generated tool name, description, and input schema. They cannot reliably tell whether a tool is read-only, destructive, or idempotent, which makes it harder to rank tools correctly and use them safely.
This is implemented in the bundled OpenAPI-to-MCP converter in two ways:
- It infers default tool behavior from the HTTP method.
- It reads explicit operation-level configuration from the OpenAPI vendor extension
x-mcp-annotations.
When both are present, explicit x-mcp-annotations values override the inferred defaults.
Complete the previous example using Admin API, ADC, or APISIX CRD to expose an OpenAPI document through the openapi-to-mcp plugin, then add annotations to the OpenAPI operations:
The previous Petstore example uses a public OpenAPI document that you cannot edit directly. To apply x-mcp-annotations, host your own OpenAPI document and update the openapi_url field in the openapi-to-mcp plugin configuration to point to that hosted document.
paths:
/users/{id}:
get:
operationId: getUser
summary: Get user information
x-mcp-annotations:
title: Get User
readOnlyHint: true
openWorldHint: false
delete:
operationId: deleteUser
summary: Delete a user
x-mcp-annotations:
title: Delete User
destructiveHint: true
Supported annotation fields:
titlereadOnlyHintdestructiveHintidempotentHintopenWorldHint
If x-mcp-annotations is not configured, the converter still applies default inference rules:
GET,HEAD, andOPTIONSmap toreadOnlyHint: trueDELETEmaps todestructiveHint: trueandidempotentHint: truePUTmaps toidempotentHint: true
After updating the hosted OpenAPI document, ask your MCP client to list tools. The following snippet shows the result.tools portion of the tools/list response:
{
"tools": [
{
"name": "getUser",
"annotations": {
"title": "Get User",
"readOnlyHint": true,
"openWorldHint": false
}
},
{
"name": "deleteUser",
"annotations": {
"title": "Delete User",
"destructiveHint": true,
"idempotentHint": true
}
}
]
}
Notes:
- Only operation-level
x-mcp-annotationsis supported. - Invalid values and unsupported fields are ignored.
summaryanddescriptionstill control the generated tool description.titleis only read fromx-mcp-annotations.title.
Troubleshooting
To diagnose issues, check the openapi-to-mcp error log at /usr/local/openapi2mcp/error.log in your gateway container or pod. Note that this log is separate from the gateway’s error log.
Known Issues
-
The error
Cannot use 'in' operator to search for '$ref' in undefinedtypically occurs when an OpenAPI v2 document is used inopenapi_url. The plugin only supports OpenAPI v3 document inopenapi_url. -
The plugin has a known parsing issue when handling
oneOfschemas in OpenAPI v3 document retrieved fromopenapi_url. In this case, the MCP client will be stuck at tool loading.